|
Cold War Warriors
NSA Surveillance Programs
Commander John Murphy, USN Ret.
 There’s something in it for everyone! There’s something in it for everyone!
The media is abuzz with stories about National Security Agency surveillance programs and Booz Allen Hamilton employee Edward Snowden’s adventures in Hawaii, China and Russia. A tale of one man’s adventure to save America and the world from the evils of big government monitoring of their cell phone calls and Email messages. Throw in images of a scantily clad young woman
luxuriating in the hero’s Hawaiian beach pad before the adventure began. Then a never ending tale being told from plush, Moscow hotels and airport lounges, that bring back memories of the Cold War. Big government run amok.
Throw in a smattering of high tech computer magic and 21st century, espionage. Its about big government’s invasion of our personal privacy- about patriots, terrorists, whistleblowers, traitors and spies. You may not understand much of what you are reading, but you can’t get enough of it. You want it and you will be getting it for some time to come! Why, because the folks who
make their living in the 24 hour news cycle, will be feeding you a new dose of it every day. This is the story that just keeps on giving. I am sure that Hollywood already has feelers out for the rights to an upcoming movie expose ‘Whistleblower … The epic tale of David versus Goliath in an age of cyber warfare’. Coming to a theater near you!
Don’t blame me …. blame the computer…
So what is it all about? As a former employee of both the National Security Agency and Booz Allen Hamilton I have thought about this a lot lately. Edward Snowden worked on NSA contracts for Booz Allen in Hawaii in 2013. Since he began his trip to Russia last June, I have been going through what psychologists call the five stages of loss and grief- denial, anger, bargaining,
depression and acceptance. I think I have just entered the acceptance stage. I see a light at the end of the tunnel- and it may be the train.
If I put my Cold War Warrior’s hat on, I would view this as a simple case of treason. You don’t work for NSA & sign oaths to safeguard the nation’s secrets and then release an unknown quantity of secrets without an expectation of retribution. Once you cross the line - it’s payback time. But I’m also beginning to accept the idea that we are in a different kind of a war. It is
not my Cold War…..or World War II where peddlers of state secrets could expect very harsh treatment if and when found guilty. Snowden’s case may very well end up in the U.S. Court system and if it does, it will be very interesting to see how it turns out.
How so? I am now trying to see this through the eyes of one living in today’s computer-dependent, high tech world. A world of instant news and self gratification. A world of the internet, blogs, Google searches, social media, credit cards, credit checks, consumer fraud and identity theft. A world that is aggressively filing away every little “factoid” that we release into the
Internet and blogosphere. And, lest you become too complacent, your friendly social network services are constantly reminding you to update your personal information or letting you know “you have new friends!”
As one who recently was the target of an internet “phishing” attack by an Eastern European site, I am a lot more scared of these folks than I am of NSA collecting my cell phone data. Especially because they’re so aggressive and unrelenting! And they all feed on each other. I NEVER gave out my Social Security Number to anyone, but I lost it
in my 2013 phishing attack. Suddenly my Social Security Number and other private information is appearing in social media and trusted credit card sites- like magic.
They say things don’t get real until they get personal
I know NSA and I trust them. As a young naval officer I helped them move from Washington D.C. to Fort Meade Maryland in1958. I worked in an office next door to infamous defectors - William Martin and Bernon Mitchell. Brilliant, young idealists who worked in one of NSA’s most sensitive, analytic organizations. Like me, they had a rudimentary understanding of the Russian
language. They were trying to improve their language skills by reading the top Soviet newspapers and journals of the day - Red Star, Ivestiya, Pravda and Ogonyek (The Lamp). Pure propaganda, but they were buying it. They became convinced that U.S. airborne surveillance programs along the periphery of the Soviet Union were immoral. Surveillance immoral? Sound familiar?

William Martin and Bernon Mitchell at their press conference in Mascow
At any rate they walked away from their desks at NSA in the Summer of 1960. The KGB Travel Agency secretly guided them from the U.S. to the USSR via Mexico on a Soviet tramp steamer. They sailed right past me at my new, NSA station in Istanbul in September 1960. In 1963, an NSA study concluded that "Beyond any doubt, no other
event has had, or is likely to have in the future, a greater impact on the Agency's security.” Oh?
And how did things work out for Martin and Mitchell? Not so well! First they were milked for all the propaganda value they had through a series of showy press conferences in Moscow. Then they were exiled to separate lives near Leningrad (St. Petersburg) and lived as second class, Soviet citizens. Obviously they couldn’t be trusted with any work of real importance to Soviet
society.
Mitchell renounced his American citizenship and died in St. Petersburg in 2001. Martin later told a Soviet newspaper that his defection had been “foolhardy”. He applied at the American consulate in Moscow for repatriation and it was denied. He also was denied a tourist visa. Somehow he got out of the Soviet Union and died of cancer in Tijuana, Mexico in 1987.
You probably can see the similarities between the Martin and Mitchell case of the 1960s and today’s Edward Snowden case. Both were triggered by a crisis of conscience over the morality of NSA surveillance programs followed by a surprise, secret journey to Russia. Then a series of press conferences before the world press- that were facilitated by a most supportive, Russian
“host” who was appalled with how the U.S. was violating its citizens’ civil rights.
Contractors in a high-tech cyber world
Also I know Booz Allen Hamilton, and I trust them. In my mind, Booz Allen set the “gold standard” for government contractors when they came to Washington in World War II to set up the Navy’s “Murmansk Run” project office. Their highly qualified staff created a series of techniques by which complex program and project management was conducted. What they called Program
Evaluation and Review Technique charts to view and control interlocking, complex activities. Goals, Milestones and Schedules in the day before computers. Techniques that later became part of the toolkit of all major businesses in the U.S.
I was a Principal at Booz Allen in the 1980s when we first set up a business area doing experimental intelligence analysis for government clients. I was hiring experienced, intelligence professionals. They were fully cleared and had long, impressive records in the intelligence world. Our government clients paired them with computer experts from major defense, hardware firms
such as TRW, HRB Singer, BTG, Lockheed, McDonnell Douglas… you name it. They built the hardware and the Booz Allen analysts challenged and tweaked the software that made them work. Frankly I was glad I was not in the business of hiring the computer people. This was a highly competitive world. One in which these folks were good and they knew it. They were always keeping their
resumes up-to-date. For the next good offer that came along. So much for corporate loyalty.
We wanted people that were “screen tuggers” not “geeks”. We wanted people that really wanted information from the computers and didn’t give a darn how they worked. I found that when working with a team of screen tuggers and geeks - you had to keep the geeks focused on the situation that you were looking for.
For example, we might be looking for indications of major, Warsaw Pact exercises. A case in point would be International Women’s Day that occurred like clock work each March. You could set your watch on it … It was good training. When the exercise did start to unfold, I found my geeks were totally lost in some technical coding work that was totally insensitive to the real
world situation. “Don't bother me… I’m busy”.
The screen tuggers were trained to try and focus the geeks on the real world events. Sometimes this was not an easy task. From these real world events came “indicators” that were plugged into the computer’s software databases. These were the early days of what was called “artificial intelligence”. They provided important real
world alerts of events that could occur in military operations such as the activation of major command posts or diplomatic facilities. This came from a sophisticated understanding of not only the chain of events but the organizations involved, and the command-and-control that existed for such events. Who was telling whom what to do and in what time sequence? Sounds easy
enough, but only if you pay careful attention to isolated events and relate them to the overall situation.
By the late 1980s we were starting to get pretty darn good at this kind of analysis, but it took a team effort of qualified intelligence analysts and geeks. I left Booz Allen Hamilton in 1990 and was comfortable in the fact that future intelligence analysts would have much better tools and software then we had in the early 1980s. Also, we constantly reminded our project staff
that the government client was always the boss. We were there to support them. Not to do their job for them. In many cases we had more experience than the client, but they still were in charge. We were a team working together on important national issues. Our government clients called our facility the Product Development Experimentation Center.
This was in the days when the intelligence community was beginning to realize the potential of personal computers to perform what was called “relational analysis”. The linking of complex, interrelated data in near-real-time that previously had been done by the human brain - when it was rested and alert. The kind of analysis you do every day now when you pose a question in a
Google search. Isn’t it amazing what pops up on your screen when you ask a carefully worded question? This is the kind of thing that Steve Jobs was working on with his NeXT computer in the early 1990s - before returning to Apple. Yes, the best and the brightest were working on relational analysis in the late ‘80s and early ‘90s - when Edward Snowden was in grade school in
Elizabeth City, North Carolina.
Computers then and now
Let us not forget that the common factor that was holding all the analytic activities together from the 1950s to today was the modern computer and spinoff technologies. I believe that the incubator for today’s modern computer was the NSA computer center in the basement of our new building at Fort Meade. It housed IBM and Cray mainframe computers stretching as far as the eye
could see. They were working on cryptanalytic tasks for the agency. You and your desktop computer are the beneficiary of the research and development done by NSA in the 1950s.
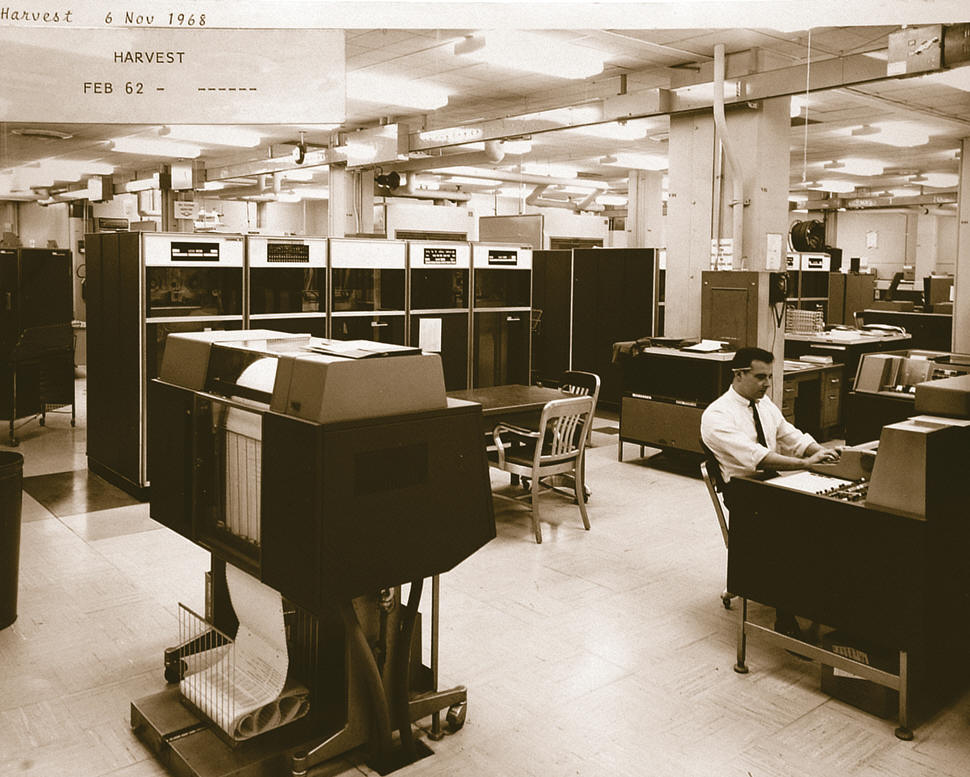
The NSA's Computer center - 1962. The computers of the time had
less computing power then today's typical smart phone
Beware of Brainiacs!
One of the dilemmas NSA and most modern computer companies face is the rapid advance of technology and the people who work with this technology on a daily basis. Call them what you want … computer scientists, IT experts, geeks, and “gamers”. I have started calling them “brainiacs”. They are a highly mobile lot and will seldom remain with any one company or organization for
very long. They are also very much in demand. Especially If they have special, government classified clearances. Top clearances mean top paychecks.
In recent studies, psychologists have noted that in some respects, such talented people have a form of autism or Asperger’s disease. A personality disorder where one is uncomfortable interacting socially, lack nonverbal communication skills (i.e. tone and pitch, body language etc.) and empathy for their peers. As high school and college students, many brainiacs fail to
achieve at levels commensurate with their abilities. They are bright, but do not earn a high school diploma. They lack confidence in their ability to achieve goals. They may have hidden disabilities. But, they make excellent “gamers” (game developers).
Remember Brainiac? He was was one of Superman’s oldest enemies in Marvel Comics. A Coluan genius who had super advanced technology at his finger tips and a brain level of 12. Whatever that meant. Brainiac roamed the universe looking for civilizations that he could add to his collection of captured worlds.
To the average person a brainiac does appear to be operating from a different planet. We don’t know how they do it, but they seem brilliant and have skills that are valuable to us mere earthlings. NSA has always had a need for Supermen and Superwomen who could cope with the seemingly unsolvable problems of the day. They needed brainiacs.
We had such a group back in the early days of NSA. We called it ADVA 03. A small group of geniuses that had an unworldly gift for breaking codes. I envied them because they had a nice, comfortable office and an impressive desk with a typewriter. But, they seldom came in to work. They only came in when specifically asked - to solve a difficult problem. Otherwise they were back
home in New England playing in the New Haven Symphony … or some such. I remember thinking “I want to be in ADVA 03. This is a good deal!”
I asked one old timer, “how do you get to be in ADVA 03?” He said “John, it seems you are either a mathematician or musician. They both make good code breakers.” I walked away thinking “I’m a musician maybe there’s hope.” But, I never made it. Maybe I played the wrong instrument? I think if I asked the same question today I would be told “mathematicians, musicians or computer
scientists”.
I’m sure there is such a group as ADVA 03 at NSA today. In fact, a recent “60 Minutes” program visited NSA and chatted with such a group. Brilliant young men and women with exceptional skills in cryptanalysis and computer science. A cyber era reincarnation of William F. Friedman, Alistair Denniston and Lambros Callimahos from World War II. The problem with brainiacs is they
are hard to control. It is like herding cats. They can wander off and get you and themselves into lots of trouble. Especially in this day and age. This was the case with my coworkers Martin and Mitchell- and I believe may be the case with young Edward Snowden.
So where do we stand in the Snowden affair?
 It is a little too early to tell. We are in chapter seven (month) of this exciting adventure (Snowden “defected” on June 10, 2013). If I had been at a desk at the FSB Center (former KGB Headquarters) in Lubyanka Square, Moscow in June 2013 I would have felt pretty good. “I can’t get
enough of this Snowden stuff! It is propaganda bonanza. America’s most secretive spy agency is spying on foreign leaders! Our Disinformation guys could not have made up such stuff! Life is good!” It is a little too early to tell. We are in chapter seven (month) of this exciting adventure (Snowden “defected” on June 10, 2013). If I had been at a desk at the FSB Center (former KGB Headquarters) in Lubyanka Square, Moscow in June 2013 I would have felt pretty good. “I can’t get
enough of this Snowden stuff! It is propaganda bonanza. America’s most secretive spy agency is spying on foreign leaders! Our Disinformation guys could not have made up such stuff! Life is good!”
As for the thousands of classified documents being released to the press? “Nothing new here. We had all that stuff from our Department 16 (Russian NSA) collection of Sprint, AT&T, Facebook and Google data. Translated - Snowden will probably be of little value to the Russian security services after his propaganda value has passed.
Just like Martin and Mitchell. “The data he is peddling is boring. We had it already”.
Legally, I have no idea where this matter is headed. If and when Edward Snowden returns to America, he will have to face the American justice system. According to press reports he did divulge classified material and he did sign oaths not to do so. Clearly a federal crime the last time I looked. His motivation for doing so is not clear. What William Martin later labeled
“foolhardy” … in his own case. Although, I can see where our Department of Justice could make a case that Snowden was aiding and abetting an enemy in the War on Terror. Also he alerted the terrorist networks of their own vulnerabilities. He has wrapped himself in the flag of a “whistleblower“. Will this somehow protect him from Federal Prison? I doubt it, but that is to be
determined.
I believe there are other Edward Snowdens out there. Young brainiacs who are just waiting for their own moment of fame. How we handle the Snowden case could send a signal to such folks. The very technology which gives the brainiacs a living… also allows them to abscond with state secrets. A small, thumb drive attached to a computer, can do a lot of damage in a few seconds. So
easy. And once the deed is done you have a worldwide organization to turn to for support - WikiLeaks. Such a deal!
Martin and Mitchell only had the KGB. The Julian Assange Travel Agency will even provide you with escort services during your travels to your country of choice - be it China, Ecuador, Venezuela or Russia. They might even hook you up with a partner such as the “The Guardian” news service in London to pre-release some of your material.
Now that the horse is out of the barn what can we do?
We need to step back and figure out what to do next. Start with a “damage assessment” - to our national security, our institutions (i.e. NSA, legal system etc.), and our civil liberties.
We have to remind ourselves that we are a nation that is at war - the War on Terror. A war that is worldwide in nature and stretches its ugly tentacles from Afghanistan to Manhattan and the streets of Boston. We must be extra diligent and willing to sacrifice for the common good - as we did in World War II. Also we must remember that is the era of 21st-century, cyber warfare.
For better or worse, information flows freely and openly across national borders. We are one world enjoying the benefits and learning the risks of modern technology. Now there might be a Trojan Horse or other spyware that has been planted inside our desktop computers, cell phones, laptops or tablets. There are bad guys out there trying to get our personal information just
because it’s fun and doable or because they can hurt us-physically or financially.
 You want to network via social networks? Update your daily life’s achievements in such convenient places as Facebook or LinkedIn or Twitter? Go-ahead, but also recognize that a worldwide network of bad guys is out there waiting to scoff up your likes and dislikes,
credit card information, credit status, Social Security number, IRS filings, bank records, personal contact information and the contact information for everyone in your Address book. Oh, and yes, even your cell phone metadata through your friendly AT&T or Sprint server sites. It’s out there … ripe for the taking. I know because I’ve been there. They’re the ones you need to
worry about … not NSA. You want to network via social networks? Update your daily life’s achievements in such convenient places as Facebook or LinkedIn or Twitter? Go-ahead, but also recognize that a worldwide network of bad guys is out there waiting to scoff up your likes and dislikes,
credit card information, credit status, Social Security number, IRS filings, bank records, personal contact information and the contact information for everyone in your Address book. Oh, and yes, even your cell phone metadata through your friendly AT&T or Sprint server sites. It’s out there … ripe for the taking. I know because I’ve been there. They’re the ones you need to
worry about … not NSA.
We should now look at the personal security issues in the Edward Snowden case. The quality of our security investigations, government contractor access to highly sensitive, classified information, improved security standards and procedures for the use of government computers. We also need to conduct a thorough review of federal and international laws relating to cybercrime
(i.e. espionage, copyright infringement, financial theft). We need to send a clear signal to other, would-be Edward Snowdens that are out there that they are playing in a very dangerous game. A game where we all could be the ultimate losers.
Read other articles by Commander John Murphy
Read other Cold War Warrior
Articles
|